Documentation Index
Fetch the complete documentation index at: https://docs.phala.com/llms.txt
Use this file to discover all available pages before exploring further.
Code Walkthrough and KT Materials
This page is an internal knowledge-transfer resource. It maps the codebase structure, traces the key request path from application to KMS, and highlights the files you’ll need to understand when contributing to dstack-cloud.Note: This document is an internal deliverable for new contributors and team members.
Guide for New Contributors
If you’re new to dstack-cloud, here’s the recommended reading order:- Understand the architecture — Read overview first to get the big picture
- Set up the development environment — Follow the README in the repository root
- Start with a simple workload — Deploy a basic nginx container on GCP using the Quick Start
- Explore the KMS — Deploy KMS and observe the bootstrap flow
- Read the attestation code — Understand how measurements are generated and verified
- Review the contracts — Understand the governance model and on-chain authorization
Repository Structure
The codebase is organized into these key areas:Core Request Paths
Understanding how a key request flows through the system is the best way to learn the codebase. Here’s what happens when an application asks KMS for a key:Key Request Flow
GCP (via Guest Agent):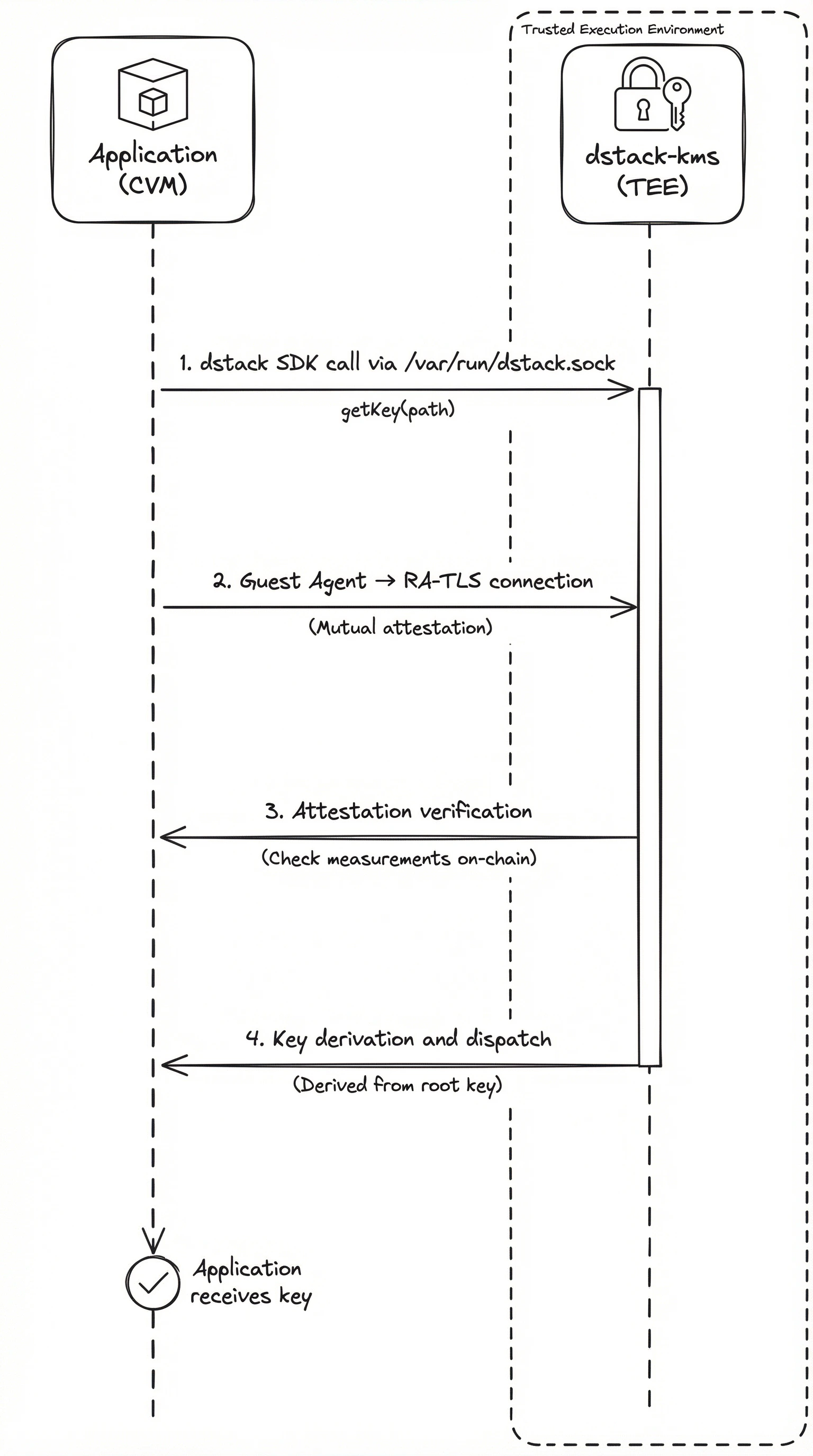
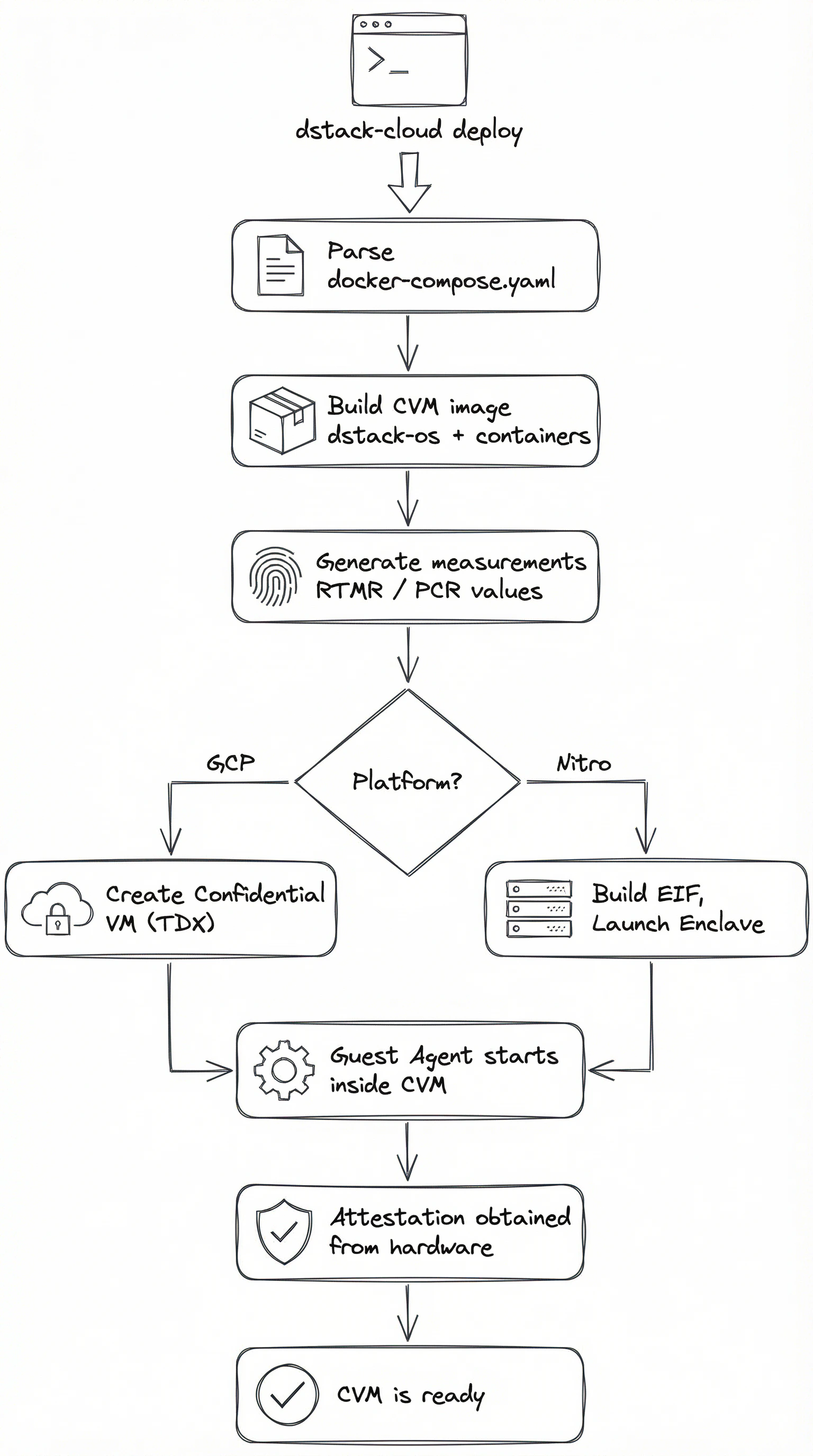
CVM Deployment Flow
When you rundstack-cloud deploy, the CLI parses your configuration and orchestrates the creation of a TEE environment. The flow differs by platform:
GCP (dstack CVM):
Attestation Module
The attestation module abstracts platform-specific hardware attestation behind a common interface. Each platform has its own module:| Platform | Module | Input | Output |
|---|---|---|---|
| GCP (TDX) | tdx-attest | TDX hardware | TDX Quote |
| AWS Nitro | nsm-attest | NSM device | Attestation Document |
| GCP (TPM) | tpm-attest | TPM device | TPM Quote |
Key Files
These are the files you’ll spend the most time in when contributing:| File | Purpose |
|---|---|
kms/src/main.rs | KMS service entry point, RPC handlers, bootstrap logic |
packages/guest-agent/src/main.rs | Guest Agent entry point, local API server |
packages/attestation/src/lib.rs | Platform-agnostic attestation interface |
cli/src/main.rs | CLI entry point, deploy/status/logs commands |
contracts/contracts/DstackKms.sol | KMS policy contract |
contracts/contracts/DstackApp.sol | Application contract |

